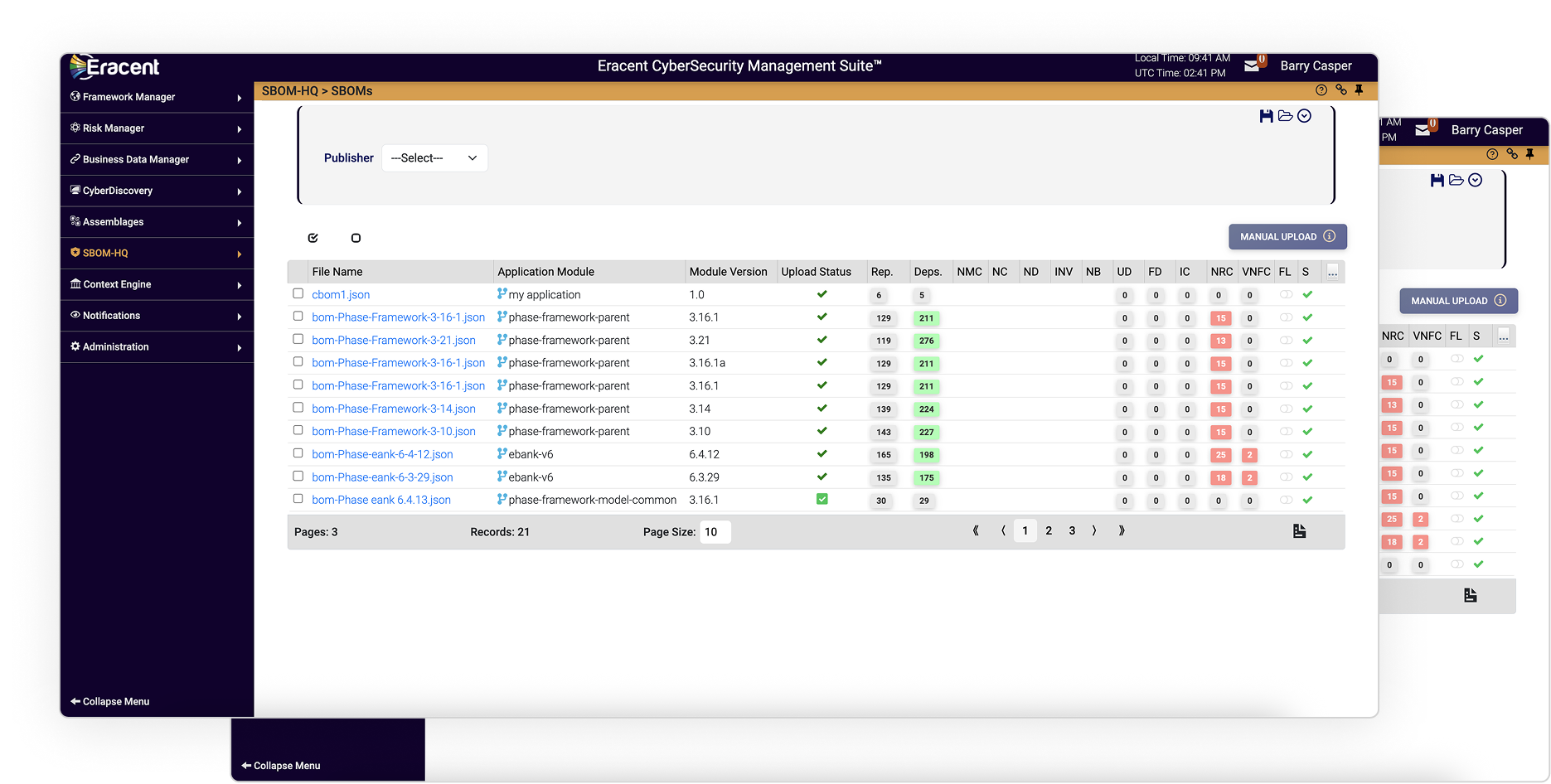
SBOM-HQ™
Utilize SBOM-HQ to manage every SBOM in one place.
Continuously monitors your environment and immediately flags new assets, configuration changes, and risks
Identify outdated libraries, unsupported dependencies, and integrity issues that could introduce vulnerabilities.
Understand where exposures exist across cloud, on-prem, and hybrid systems.
Connecting discovery, governance, and risk operations into one actionable intelligence framework.

Automatically generate and enrich SBOMs within your CI/CD pipeline, allowing security teams to detect and assess risk as vulnerabilities emerge—without slowing development.

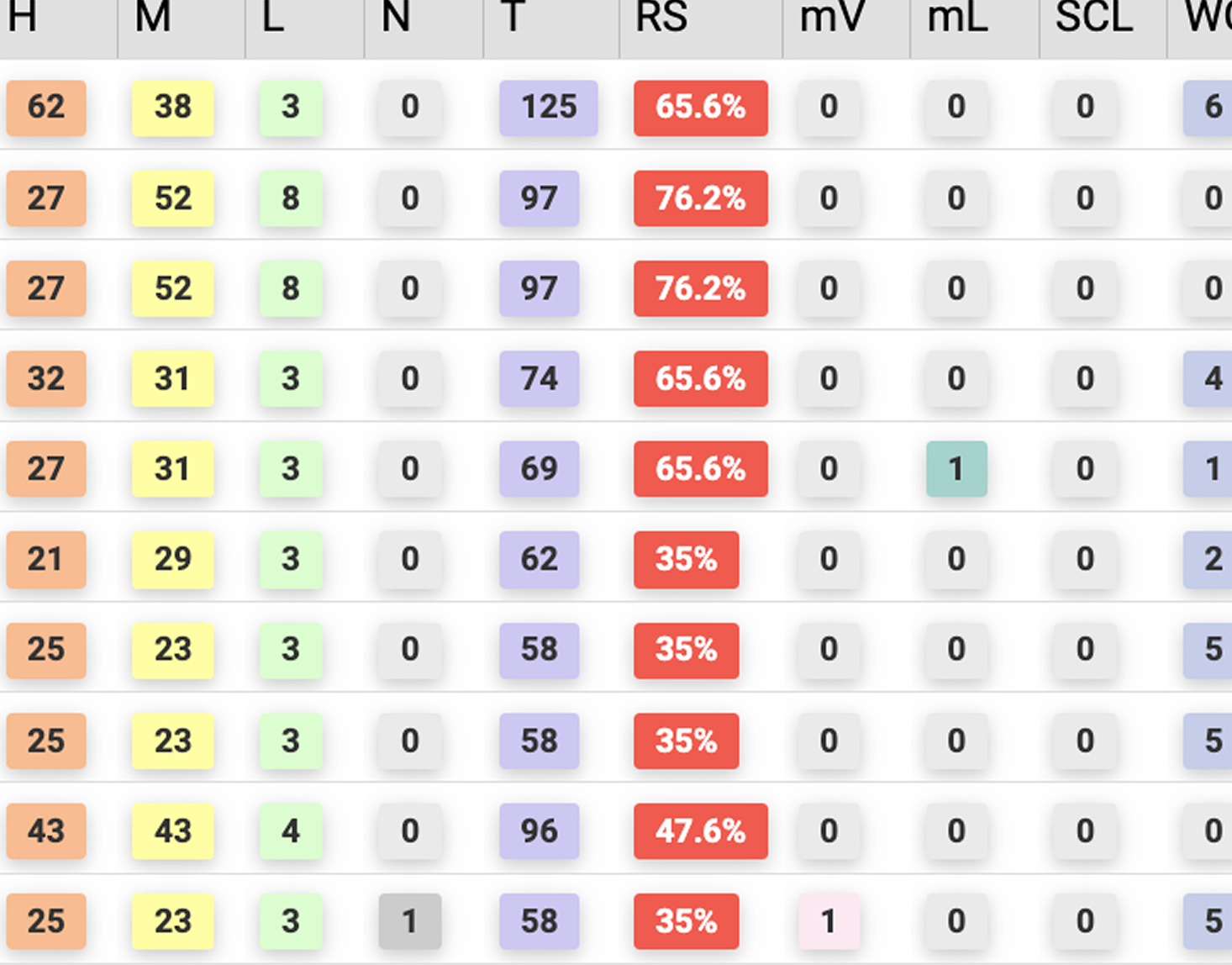
Quickly identify which applications, components, and dependencies are affected by new CVEs or security advisories, including transitive dependencies often missed by traditional tools.

Move beyond raw severity scores by prioritizing remediation based on real-world exposure, asset criticality, and business context—so teams focus on the risks that matter most.

Continuously monitor SBOMs across versions and releases to understand how software changes introduce, reduce, or shift risk throughout the lifecycle.

Trace vulnerabilities from open-source components through builds, deployments, and runtime environments, providing complete visibility from source to endpoint.

Maintain clear, auditable records of software components and risk posture to support regulatory requirements, internal governance, and security framework alignment.
Data is enriched, normalized, and validated with intelligent context — licensing data, product metadata, end-of-life timelines, vulnerability references.
SBOM-HQ unifies discovery, cleans the data, and surfaces what’s vulnerable—so you know exactly where to act.
Build secure software with real-time visibility into open-source and third-party risk.
Understand software supply chain risk before purchase, renewal, or vendor approval.
Know what software is running across your environment—and where vulnerabilities live.
A consolidated view of every component detected across your applications, including versions, dependencies, and risk indicators.
Provides one consistent foundation.
Surfaces blind spots across every stage.

Clean, consistent component data for clarity.

See impact across versions and dependencies.

Highlight the most critical issues first.
Deliver actionable insights for faster response.